What Is User and Entity Behavior Analytics (UEBA)?
User and Entity Behavior Analytics, commonly known as UEBA, is a cybersecurity technology that uses machine learning, statistical modeling, and advanced data analysis to detect unusual behavior patterns across users, devices, and systems within an organization. Unlike traditional security tools that rely on static rules or known threat signatures, UEBA builds a dynamic baseline of normal activity and flags deviations that could indicate insider threats, compromised accounts, or advanced persistent threats.
The term “entity” extends the scope significantly beyond just human users. UEBA also tracks endpoints, applications, servers, cloud workloads, and connected devices. This broader coverage makes it far more powerful than its predecessor, User Behavior Analytics, which focused exclusively on monitoring people rather than the full spectrum of interacting systems and assets.
Organizations across finance, healthcare, government, retail, and technology sectors are rapidly adopting UEBA solutions to close the detection gaps that traditional security information and event management tools leave open. As cyberattacks grow increasingly sophisticated and insider threats become harder to detect manually, the demand for intelligent behavioral analytics has reached an all-time high in 2026.
Why UEBA Software Is Essential in 2026
The modern threat landscape has transformed dramatically. Attackers no longer simply break through perimeter defenses. They move laterally through networks over extended periods, escalate privileges gradually, and deliberately mimic legitimate user behavior to avoid triggering conventional detection systems. Traditional perimeter-based security controls are fundamentally inadequate against this approach.
The expansion of artificial intelligence-powered attack tools has made this problem significantly worse entering 2026. Cybercriminals are now using AI to craft more convincing phishing campaigns, automate credential stuffing at scale, and even simulate legitimate user behavioral patterns to evade detection. Against this backdrop, only a platform that deeply understands normal behavior and continuously measures deviation from it can keep pace.
UEBA software addresses these challenges directly. By continuously analyzing behavioral data across the entire environment, it detects threats that would otherwise remain invisible for weeks or months. The average dwell time of an attacker inside a compromised network has historically been measured in weeks, and modern UEBA dramatically compresses that detection window.
Key drivers behind accelerating UEBA adoption in 2026 include the explosive growth of remote and hybrid work arrangements, deep reliance on multi-cloud infrastructure, increasingly strict data privacy regulations such as GDPR and its regional equivalents, the proliferation of AI-assisted cyberattacks, and growing insider threat risks from both negligent and malicious employees. Security teams are also under intense pressure to reduce alert fatigue, and UEBA helps by surfacing only the highest-risk behavioral anomalies for human review.
Core Features to Look for in UEBA Software
Before evaluating specific platforms, understanding what separates genuinely effective UEBA software from average solutions is essential. These are the most critical capabilities to evaluate.
Behavioral Baseline Creation The foundation of any UEBA platform is its ability to establish what normal looks like for each user and entity over time. This requires collecting historical data, building peer group comparisons, and continuously refining baselines as legitimate behavior evolves within the organization.
Machine Learning and AI-Driven Detection Leading UEBA tools in 2026 use unsupervised machine learning models that require no manual rule configuration. They learn continuously, adapt as behavioral patterns shift, and reduce both false positives and false negatives over time. Platforms now increasingly incorporate large language model capabilities to enhance contextual understanding of threat scenarios.
Risk Scoring and Prioritization A strong UEBA platform assigns dynamic risk scores to users and entities based on cumulative behavioral signals across multiple data sources. This allows security teams to focus attention on the highest-priority threats rather than investigating every individual alert.
Integration with SIEM, SOAR, and Identity Platforms UEBA is most effective when it operates as part of a larger, interconnected security ecosystem. Look for platforms that integrate natively with major SIEM solutions, security orchestration and automated response tools, identity governance platforms, and endpoint detection and response systems.
Insider Threat Detection Top-tier UEBA platforms are specifically tuned to detect insider threats, including data exfiltration attempts, privilege misuse, unauthorized access to sensitive files, off-hours system access, and suspicious behavioral patterns that correlate with employee termination events or organizational stress indicators.
Cloud and Hybrid Environment Support As organizations operate across AWS, Azure, Google Cloud, and multiple SaaS applications simultaneously, UEBA tools must extend full behavioral visibility into cloud environments and hybrid architectures. Coverage gaps in cloud telemetry represent dangerous blind spots.
Identity Threat Detection and Response A major evolution in 2026 is the convergence of UEBA with identity threat detection and response capabilities, specifically targeting attacks against authentication infrastructure, privileged accounts, and identity governance systems.
Generative AI-Assisted Investigation The best platforms now include natural language query interfaces, automated investigation summaries, and AI-generated threat narratives that dramatically reduce the time analysts spend manually reconstructing attack timelines.
Forensic Investigation Capabilities When an alert triggers, security analysts need deep investigative tools to trace the full timeline of suspicious activity, correlate events across systems, visualize attack chains, and gather evidence suitable for incident response proceedings or legal investigations.
Best User and Entity Behavior Analytics Software in 2026
1. Microsoft Sentinel with UEBA
Microsoft Sentinel remains one of the most widely deployed cloud-native SIEM and SOAR platforms in the world, and its deeply integrated UEBA capabilities continue to be a central reason for its dominance in enterprise security operations. The platform’s behavioral analytics engine aggregates identity signals from Microsoft Entra ID, Microsoft 365, Defender for Endpoint, and a broad range of third-party data connectors to build comprehensive user and entity profiles.
Sentinel’s UEBA module uses machine learning to identify lateral movement, credential compromise, account takeover attempts, and insider threat patterns across cloud and hybrid environments. What makes it exceptionally powerful in 2026 is its deep integration with Microsoft Security Copilot, the generative AI layer that allows analysts to query behavioral data in plain English, automatically summarize suspicious activity timelines, and generate incident reports with minimal manual effort.
The platform’s threat intelligence integration enriches behavioral findings with global context, allowing the system to correlate observed anomalies with known attacker tactics and techniques mapped to the MITRE ATT&CK framework. Security teams benefit from unified investigation experiences where a single alert expands into a full behavioral timeline across every connected data source.
Sentinel’s consumption-based pricing model makes it accessible at different organizational scales, though data ingestion costs can escalate significantly in high-volume environments. Its tight coupling with the Microsoft security ecosystem does mean that organizations running competing endpoint or identity platforms may not extract the full depth of behavioral context that Microsoft-first environments enjoy.
Best For: Microsoft-centric enterprises, cloud-heavy environments, organizations seeking native SIEM and UEBA integration with generative AI investigation capabilities.
2. Splunk Enterprise Security with Splunk UBA
Splunk has long been the gold standard for enterprise security analytics, and its combined Enterprise Security and User Behavior Analytics offering continues to represent one of the most mature and capable UEBA deployments available. Splunk UBA operates as a complementary product alongside Enterprise Security, applying unsupervised machine learning models to the telemetry that Splunk already collects from across the environment.
Splunk UBA uses more than 65 anomaly detection models and over 350 pre-built threat detection use cases out of the box, covering scenarios ranging from compromised account activity and lateral movement to data exfiltration and privilege escalation chains. Its threat chain analytics capability visualizes kill chain progressions in a way that helps analysts quickly understand the full scope and intent of a suspected attack rather than reacting to isolated alerts.
The platform’s most significant advantage is its unmatched data ingestion flexibility. It can pull behavioral signals from network traffic, endpoint telemetry, authentication logs, cloud provider activity, application performance data, and virtually any structured or unstructured log source. This breadth of coverage makes it particularly valuable for large, complex environments where behavioral context must be assembled from dozens of disparate data sources.
In 2026, Splunk has continued to advance its AI-assisted investigation capabilities, with the Splunk AI Assistant enabling analysts to interact with behavioral data conversationally. The integration with Cisco’s broader security portfolio following the acquisition has also expanded Splunk’s network telemetry capabilities, enriching behavioral analytics with deeper network-level context.
Splunk carries significant licensing costs and requires experienced administrators to manage effectively, making it less accessible for organizations without dedicated security engineering resources.
Best For: Large enterprises, mature security operations centers, organizations with complex multi-source data environments requiring comprehensive behavioral coverage.
3. Securonix
Securonix is a purpose-built UEBA and next-generation SIEM platform that has maintained consistent recognition from leading analyst firms for the sophistication of its behavioral detection capabilities. Designed from the ground up with behavioral analytics at its core rather than bolted on afterward, Securonix has a structural advantage over platforms that added UEBA capabilities to existing architectures.
The Securonix platform uses big data infrastructure and advanced machine learning to analyze hundreds of billions of events per day across large enterprise deployments. Its threat content library covers an extensive range of behavioral scenarios including cloud account compromise, data exfiltration through email or removable media, privileged account abuse, third-party vendor risk, and complex multi-stage attack chains that unfold over extended periods.
Securonix Spotter, the platform’s natural language search interface, allows analysts to query behavioral data using conversational queries rather than complex search syntax. This capability has matured significantly in 2026, with enhanced generative AI features enabling automatic threat narrative generation, recommended investigation steps, and contextual enrichment from integrated threat intelligence feeds.
The platform’s compliance reporting capabilities make it particularly valuable for organizations in regulated industries. It supports audit requirements for SOX, HIPAA, PCI DSS, NIST, and numerous other frameworks with pre-built report templates and automated evidence collection workflows.
Securonix’s cloud-native architecture allows it to scale dynamically with organizational data volumes, and its open integration framework supports connections with a broad range of identity, endpoint, cloud, and network security tools.
Best For: Regulated industries, large enterprises seeking purpose-built UEBA, organizations running advanced insider threat programs requiring sophisticated behavioral modeling.
4. Varonis Data Security Platform
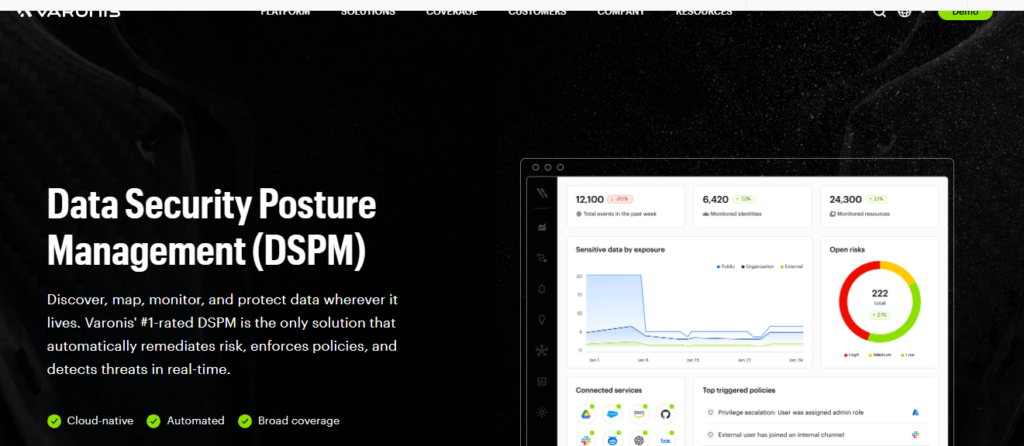
Varonis approaches UEBA from a distinctly data-centric perspective, making it uniquely valuable for organizations whose primary security concern is protecting sensitive data assets rather than just detecting network-level threats. Rather than beginning with network traffic or endpoint telemetry, Varonis starts with data itself, mapping who has access to what, tracking who is actually using it, and flagging behavior that deviates from established patterns of data access and handling.
The platform automatically classifies sensitive data across file systems, cloud storage repositories, email platforms, SharePoint environments, and collaboration tools, then builds behavioral models around how that data is accessed, modified, and shared over time. When a user begins accessing an unusual volume of sensitive files, moves data to a personal cloud storage account, accesses classified documents outside their normal working hours, or begins downloading bulk records shortly before an anticipated resignation, Varonis detects and alerts on that activity in near real time.
Varonis has made significant advances in its automated remediation capabilities entering 2026. The platform can now revoke excessive permissions, disable compromised accounts, quarantine suspicious files, and trigger automated response workflows without requiring manual intervention, substantially reducing mean time to respond for data-related incidents.
Its data access governance capabilities also make Varonis valuable beyond pure threat detection. Organizations use it to identify and eliminate excessive permissions, enforce least-privilege access, and maintain continuous visibility into who can access their most sensitive information assets.
Best For: Data security-focused organizations, companies protecting intellectual property or regulated data, environments with complex data governance and least-privilege enforcement requirements.
5. Exabeam
Exabeam has established itself as one of the most innovative and analyst-recognized vendors in the UEBA and next-generation SIEM market. Its Security Operations Platform places behavioral analytics at the center of the entire security operations workflow, from initial detection through investigation and case closure.
Exabeam’s Smart Timelines feature remains one of the most operationally impactful capabilities in the UEBA market. It automatically assembles a complete chronological view of a user’s or entity’s activity during any suspicious period, pulling relevant events from all connected data sources and presenting them in a unified, easy-to-interpret timeline. Security analysts report significant reductions in investigation time when using this feature compared to manually correlating logs across multiple platforms.
The platform supports over 500 data source integrations and includes more than 1,900 pre-built detection rules aligned to the MITRE ATT&CK framework, covering both initial access techniques and post-compromise behaviors. In 2026, Exabeam has expanded its AI Analyst capability, which can autonomously triage incoming alerts, determine whether they represent genuine threats, and generate written investigation summaries that human analysts can review and act upon.
Exabeam’s case management capabilities allow security teams to track investigations from initial alert through to resolution with full audit trails, which is particularly valuable for organizations with compliance reporting obligations. Its New-Scale SIEM architecture is purpose-built for cloud-scale data volumes, addressing one of the longstanding criticisms of legacy SIEM platforms.
Best For: Organizations modernizing legacy SIEM infrastructure, teams prioritizing rapid investigation workflows, mid-market and enterprise organizations seeking modern behavioral analytics without legacy architectural constraints.
6. CrowdStrike Falcon Identity Threat Protection
CrowdStrike’s approach to UEBA is identity-first, and in 2026 this positioning has proven prescient as identity-based attacks have become the dominant vector in major breaches. Falcon Identity Threat Protection ingests Active Directory telemetry, Azure AD and Entra ID signals, and authentication data from across the environment to build behavioral profiles and detect credential-based threats in real time.
The platform excels at detecting advanced credential abuse techniques including pass-the-hash, Kerberoasting, golden ticket and silver ticket attacks, DCSync attacks, and password spray campaigns. These are precisely the techniques most commonly used in ransomware intrusions and nation-state operations, and CrowdStrike’s deep specialization in this area gives it detection capabilities that more generalist platforms struggle to match.
What gives CrowdStrike Falcon Identity Threat Protection a unique advantage is its integration with endpoint telemetry from the broader Falcon platform. By correlating identity-based behavioral anomalies with endpoint activity data, it can detect scenarios where compromised credentials are being used from unusual endpoints, combined with suspicious process executions or lateral movement indicators that endpoint detection has already flagged.
The Falcon platform’s CrowdStrike Falcon Adversary OverWatch team also feeds real-world threat intelligence from active intrusion campaigns directly into the platform’s detection models, ensuring that behavioral baselines and alert logic reflect the latest attacker tradecraft.
Best For: Organizations facing advanced persistent threats, enterprises with mature endpoint security programs wanting unified identity and endpoint behavioral analytics, security teams focused on defeating credential-based attack chains.
7. Securonix vs. IBM QRadar with UEBA
IBM QRadar remains one of the most established SIEM platforms in the enterprise market, and its UEBA capabilities have matured considerably in recent years. QRadar UEBA adds a behavioral analytics layer on top of QRadar’s existing extensive log and network flow collection infrastructure, enriching traditional correlation rules with machine learning-based anomaly detection and risk scoring.
The platform profiles users based on their typical access patterns, peer group behavior, geographic access locations, and historical baselines accumulated over time. When deviations are detected, they are scored and correlated with existing offense data within QRadar, reducing noise and surfacing only the most contextually meaningful threats for analyst review.
In 2026, IBM has accelerated integration between QRadar and its watsonx AI platform, introducing generative AI capabilities that allow analysts to interact with behavioral data more intuitively and receive AI-generated investigation guidance. The IBM Threat Intelligence platform integration also enriches behavioral findings with global threat context automatically.
QRadar’s deep integration with IBM’s broader security portfolio, including IBM Guardium for database activity monitoring, IBM Verify for identity governance, and IBM MaaS360 for mobile management, creates a comprehensive behavioral visibility layer across a wide range of enterprise data assets. Organizations already running QRadar as their primary SIEM can extend into UEBA without rebuilding their security data infrastructure.
Best For: Existing QRadar customers, enterprises with complex compliance and audit requirements, large organizations wanting a mature, well-supported platform with deep IBM ecosystem integration.
8. Gurucul
Gurucul has built a strong and differentiated position in the UEBA market through its combination of advanced machine learning capabilities, open data architecture, and flexible deployment options that reduce vendor lock-in concerns. Unlike many competitors that require organizations to store behavioral data within the vendor’s own infrastructure, Gurucul allows enterprises to ingest and retain data within their own data lakes while still applying Gurucul’s behavioral analytics models against it.
The platform offers more than 2,500 machine learning models spanning identity and access management, insider threat detection, fraud prevention, application security, and supply chain risk use cases. This breadth allows Gurucul to serve multiple organizational stakeholders simultaneously, with security operations, fraud management, and compliance teams all drawing value from a single behavioral analytics deployment.
Gurucul’s REVEAL platform, enhanced significantly in 2026, incorporates a security data lake architecture that consolidates telemetry at scale while keeping storage and processing costs manageable. Its unified behavioral analytics approach means organizations do not need separate tools for different threat scenarios, reducing integration complexity and operational overhead.
The platform is often chosen by organizations that have hit the analytical limits of SIEM-based detection and require more sophisticated machine learning capabilities without the disruption of replacing their entire security data infrastructure.
Best For: Data sovereignty-conscious organizations, enterprises needing flexible deployment options, organizations requiring unified behavioral analytics across security and fraud use cases at scale.
9. Forcepoint Insider Threat
Forcepoint takes a distinctly human-centric approach to UEBA, emphasizing understanding user intent and risk context rather than purely detecting technical anomalies in system logs. Its Insider Threat platform combines behavioral analytics with content-aware data loss prevention capabilities, providing holistic visibility into both the technical indicators and the contextual signals that precede serious insider incidents.
The platform monitors activity across web browsing, email communications, file transfer activity, USB and removable media usage, print activity, and cloud application interactions, building a complete picture of how employees interact with sensitive information across every channel. Its psychographic risk modeling approach factors in organizational stress indicators, behavioral pattern changes correlated with HR events, and contextual signals that purely technical analysis would miss entirely.
Forcepoint’s Privacy-First architecture, a key differentiator in regulated and privacy-sensitive environments, allows organizations to implement behavioral monitoring with graduated disclosure controls. Investigators only see the full detail of an employee’s activity when a defined risk threshold is crossed, addressing employee privacy concerns and legal requirements around workforce monitoring in jurisdictions with strict privacy laws.
Best For: Government agencies and defense contractors, financial institutions, high-security organizations that require combined UEBA and data loss prevention capabilities, environments operating under strict employee privacy regulations.
10. LogRhythm UEBA
LogRhythm has maintained a consistent and respected presence in the SIEM and behavioral analytics market, and its UEBA capabilities remain tightly integrated within its unified security operations platform. LogRhythm UEBA adds advanced behavioral analytics to the platform’s existing log management, network monitoring, and threat detection capabilities without requiring separate product deployments or complex integration work.
The solution profiles user and entity behavior across endpoints, network traffic, and log data to identify anomalies that signature-based detection would miss. Automated response playbooks allow smaller security teams to handle alerts efficiently, triggering containment actions automatically when behavioral risk thresholds are breached rather than waiting for manual analyst review.
LogRhythm’s strength in the mid-market segment stems from its combination of genuine enterprise-grade UEBA capabilities with a deployment and management experience that does not require the large dedicated security engineering teams that some enterprise platforms demand. Its pre-built compliance reporting for common frameworks also reduces the burden on organizations that need to demonstrate regulatory adherence without building custom reporting workflows.
Best For: Mid-market organizations, security teams with limited headcount, companies wanting integrated SIEM and UEBA behavioral analytics managed within a single unified platform.
How to Choose the Right UEBA Software for Your Organization
Selecting the right UEBA platform requires thoughtful evaluation across multiple dimensions. Here is a structured framework for making the right decision.
Identify Your Primary Threat Scenarios Start by defining which threat scenarios concern you most. Are you primarily worried about insider threats, external attackers using stolen credentials, data exfiltration, cloud account compromise, or advanced multi-stage intrusions? Different UEBA platforms have meaningfully different strengths, and aligning your selection to your actual risk profile produces significantly better outcomes than choosing based on general market reputation alone.
Audit Your Existing Data Sources UEBA is only as effective as the behavioral telemetry it can analyze. Map your current data sources, including authentication logs, endpoint telemetry, network flow data, cloud provider logs, and application activity. Identify which platforms have the best connectors for your specific environment and which ones would require significant custom integration work.
Evaluate Integration Requirements Assess which existing security platforms your UEBA solution must integrate with, including your SIEM if it is separate, your SOAR platform, your identity governance system, and your endpoint security tools. Poor integration creates visibility gaps and undermines the platform’s ability to correlate behavioral signals across the full environment.
Consider Deployment Model Requirements Some organizations prefer cloud-native SaaS deployments for scalability and reduced operational overhead. Others require on-premises or hybrid deployments due to data residency requirements, air-gapped network constraints, or regulatory restrictions on sending certain data to external cloud services. Confirm that your preferred deployment model is fully supported before shortlisting vendors.
Assess Machine Learning Sophistication Not all machine learning implementations are equally effective. During vendor evaluations, ask specifically about the algorithms used, how models are trained and updated, how the platform handles behavioral drift over time, and what false positive rates look like in environments comparable to yours. Require proof of concept deployments in your own environment with your own data before making a final decision.
Calculate Total Cost of Ownership UEBA platforms vary enormously in cost depending on data volume, the number of users and entities monitored, and deployment complexity. Factor in licensing fees, implementation costs, integration development work, training requirements, and ongoing management overhead when building a complete cost comparison.
Evaluate Vendor Stability and Roadmap In a market that is consolidating through acquisitions and partnerships, assess each vendor’s financial stability, their integration roadmap with the platforms you already run, and the frequency and quality of their threat content updates. A technically strong platform with poor long-term vendor stability creates operational risk.
UEBA vs. SIEM: Understanding the Distinction in 2026
The line between UEBA and SIEM has blurred considerably in 2026 as vendors have converged the two categories into unified security operations platforms. However, understanding the fundamental distinction remains important for evaluating solutions effectively.
Traditional SIEM platforms collect and correlate log data based on predefined rules and known attack signatures. They excel at detecting known threat patterns and satisfying compliance logging requirements. Their fundamental limitation is that they struggle to detect unknown threats, complex multi-stage attacks that unfold slowly over time, and subtle behavioral anomalies that do not match any existing rule definition.
UEBA fills this critical gap by analyzing behavior over time using machine learning rather than static rules. It can detect threats that have never been seen before purely because the observed behavior deviates from established norms, even without any matching signature or rule.
Most enterprise organizations in 2026 operate unified platforms where SIEM and UEBA capabilities are deeply integrated rather than deployed separately. Platforms like Microsoft Sentinel, Exabeam, Securonix, and LogRhythm have effectively merged the two disciplines into a single operational experience, combining comprehensive log management and compliance capabilities with continuous behavioral analysis and machine learning-driven anomaly detection.
UEBA in the Context of Zero Trust Architecture
Zero Trust security architecture, now widely adopted across enterprise environments, operates on the principle of never trust and always verify. UEBA is not merely a complement to Zero Trust in 2026 but has become a foundational component of continuous verification at the post-authentication layer.
In a Zero Trust framework, successfully completing multi-factor authentication grants access but does not permanently establish trust. UEBA provides the ongoing behavioral verification layer that continuously monitors whether authenticated users and devices are behaving consistently with their assigned roles, historical patterns, and contextual expectations. When behavioral risk scores elevate above defined thresholds, Zero Trust policy engines can automatically step up authentication requirements, restrict session permissions, or terminate access entirely without requiring manual security analyst intervention.
This integration of UEBA with Zero Trust policy enforcement represents one of the most significant operational advances in enterprise security architecture entering 2026, transforming behavioral analytics from a detection tool into an active access control mechanism.
UEBA and Regulatory Compliance in 2026
The regulatory compliance dimension of UEBA has grown substantially in importance as data privacy laws and cybersecurity regulations have multiplied globally. Regulations and security frameworks consistently require organizations to implement robust monitoring controls around privileged user access, sensitive data handling, and unauthorized access attempts.
UEBA platforms provide the automated monitoring, anomaly detection, behavioral audit trails, and reporting capabilities that help organizations demonstrate compliance with NIST Cybersecurity Framework, ISO 27001, SOC 2, HIPAA, GDPR, NIS2, and numerous sector-specific regulatory requirements. Their ability to generate detailed, timestamped reports on user activity and access patterns makes them essential tools during regulatory audits and incident investigations where organizations must demonstrate due diligence in monitoring for insider threats and unauthorized access.
The European Union’s NIS2 Directive, which entered enforcement in 2024, has significantly accelerated UEBA adoption among organizations operating in EU member states by introducing explicit requirements for advanced monitoring and threat detection capabilities that traditional security tools cannot satisfy on their own.
Emerging Trends in UEBA Technology for 2026 and Beyond
The UEBA market continues to evolve at an accelerating pace. Several key trends are defining the direction of behavioral analytics technology through 2026 and into the coming years.
Generative AI Integration Across the Investigation Workflow Every leading UEBA vendor has now integrated generative AI capabilities into investigation workflows. Analysts can query behavioral data in natural language, receive automatically generated threat narratives, and get AI-recommended investigation steps that guide them through complex incidents without requiring deep platform-specific expertise. This capability is dramatically reducing the skill ceiling required to operate advanced UEBA platforms effectively.
AI-on-AI Detection Challenges One of the most significant emerging challenges in 2026 is detecting attacks orchestrated by AI systems that deliberately study and mimic normal behavioral patterns to evade detection. UEBA vendors are responding by developing second-order behavioral models that detect the subtle signatures of AI-generated behavioral mimicry, a technically demanding problem that is driving significant research and development investment across the industry.
Identity Threat Detection and Response Convergence UEBA capabilities are converging with identity threat detection and response as a distinct security discipline, focusing specifically on protecting identity infrastructure, authentication systems, and privileged access mechanisms from sophisticated attacks that traditional behavioral models were not specifically designed to address.
Autonomous Security Operations Integration The most advanced UEBA platforms are evolving beyond alert generation into autonomous response capabilities, dynamically adjusting user access permissions in real time based on behavioral risk scores, automatically containing suspected compromised accounts, and triggering full incident response workflows without human initiation for the clearest threat scenarios.
Supply Chain and Third-Party Risk Behavioral Monitoring As supply chain attacks have remained a persistent and devastating threat vector, UEBA platforms are expanding their modeling scope to include behavioral profiling of third-party vendors, contractors, and service accounts that interact with enterprise environments, extending the same continuous behavioral verification applied to internal users to the external entities that access organizational systems.
Final Thoughts
https://en.wikipedia.org/wiki/Software_analyticsSelecting the best user and entity behavior analytics software is among the most consequential cybersecurity decisions an organization can make in 2026. The threat landscape has evolved to a point where signature-based detection, perimeter controls, and rule-driven SIEM correlations are simply insufficient to protect against the sophisticated, slow-moving, behaviorally aware attacks that characterize today’s most serious breaches.
The right UEBA platform fundamentally transforms an organization’s security posture from reactive to proactive, enabling security teams to detect sophisticated threats earlier in the kill chain, compress investigation timelines dramatically, and reduce the overall probability and impact of both insider incidents and external intrusions.
Microsoft Sentinel offers the strongest integrated experience for Microsoft-centric enterprises. Splunk delivers unmatched data ingestion flexibility and analytical depth for large security operations centers. Securonix and Exabeam represent the strongest purpose-built behavioral analytics platforms for organizations wanting UEBA at the core of their security operations. Varonis stands alone for data-centric security programs. CrowdStrike leads for identity-first threat detection. Gurucul offers the greatest deployment flexibility. And LogRhythm delivers accessible enterprise-grade UEBA for mid-market organizations with leaner security teams.
The ideal starting point is always a clear assessment of your primary threat scenarios, your existing data sources, and your integration requirements. With those foundations defined, the platforms reviewed in this guide provide a comprehensive shortlist from which any organization can identify the solution best aligned to its specific security needs, operational constraints, and risk tolerance in 2026.

Usman Hakim is an SEO specialist at RankWithLinks, focusing on link building and organic growth. He helps brands improve search rankings through white-hat strategies, including guest posting and authority backlinks.